A challenging time for data centre cybersecurity

The global shift towards cloud network architecture and data centre colocation as a service has laid considerable challenges at the feet of data centre operators in the last few years. Traditional security systems that use firewalls to keep threats at bay are no longer sufficient. “Think of a castle in a medieval city. To protect it from the outside world, you’d have this wall that over time would get taller and thicker,” explained Vladimir Gotsev, Director of Engineering at tech firm Netrix, in a recent interview with the Chicago Business Journal. “That was pretty effective as long as everyone lived inside the castle.”
Today, of course, the acceleration of cloud-based data centres, coupled with the accelerated growth of the internet of things (IoT), has changed all that. Companies are increasingly choosing to store sensitive and proprietary information remotely, in data centres operated by third parties. These third parties are then responsible for safeguarding this valuable information, and today the number of ways for malicious actors to gain access to that information is increasing exponentially. 2019 was a record-breaking year for both mega breaches and smaller scale hacks. In the first half of the year alone there were more than 3,800 publicly disclosed breaches which compromised 4.1bn records - a 54% increase year-on-year.
2020 promises to be an even tougher year for data centre operators, as the global COVID-19 pandemic drives a global work-from-home experiment on an unprecedented scale. According to a recent Gallup study, in three weeks, the percentage of employees working from home doubled, from 31% to 62%, and 52% of managers said they would allow their employees to work remotely more often. According to Gotsev, this means that companies are going to have to completely rethink their approach to security, as sensitive data becomes increasingly accessible through home and mobile devices. “Cloud-enabled organisations need cloud-delivered security,” he said.
This month, Data Centre Magazine explores the challenges facing industry operators today, and some of the strategies that will help them deliver a more secure experience to their user bases.
Only human
In a 2019 report by IBM and the Ponemon Institute, 49% of data breaches were found to have been the result of either system glitches or human error. As the technology powering cybersecurity becomes increasingly powerful, the human element is increasingly being exposed as the weak link in a network’s armour.
Ross Thomas, an IT administrator at the SSL Store, suggests that regular permission auditing to control who has virtual access to servers is an essential tool that data centre operators should be employing. “Permission auditing is crucial to make sure that access is only delegated to those that need it. Root users can be very dangerous as they are able to make any changes or execute any code or processes. But, root users are necessary. Assigning processes, tasks, etc., to the correct user is the absolute safest way to delegate processes,” he explained in a recent interview. “When personnel leave an organisation, there should be proper evaluation of their status in all systems to determine if they have access even if it is not through the front door.”
Email has been found to be the most common entry point for malicious actors outside the organisation. Phishing is by far the most commonly exploited attack vector. Introducing security training both inside and outside data centre organisations can be an effective tool in the pursuit of lowering these risks.
Data centres are only as strong as their weakest points
While data centre cyber security budgets and plans often account for encryption, firewalls and physical security, these measures often don’t extend to all aspects of a data centre network. A recent piece by Cybersecurity Insiders found that, “Power systems, which happen to be the most critical infrastructure of a data center are sadly the most overlooked architecture by Cybersecurity teams.”
Commonly, power systems are “protected” from failure by redundant backup systems and physical security. While this is an effective way to prevent uptime disruption, these measures often aren’t enough to stave off targeted threats. The software controlling these systems is often vulnerable to cyber attack, particularly through IoT, as these systems are often heavily reliant on smart sensor networks.
“So, a malicious cyber actor or a military agency of a nation can easily take control of the device and interrupt the power to a data center or a specific server on a network- eventually leading to a business disruption”, said Bob Pruett, Security Field Solutions Executive at SHI International. Data centres looking to resist external threats should take care to protect their physical systems from digital attacks if they wish to avoid these kinds of disruptions.
The six most common types of cyber attack on data centres
- Hacking and Malware: This involves actors moving directly and indirectly against a data centre’s security network via malicious software including spyware, ransomware, viruses and worms.
- Phishing: Involves the use of fraudulent communications that appear to come from a reputable source, typically via email. Phishing is the most common form of attack and takes advantage of companies with weak security training programs.
- Man-In-The-Middle (MitM) Attacks: These attacks involve bad actors inserting themselves into a two-party transaction in order to extract data or money. These attacks usually happen through unsecure public Wi-Fi networks or malware, something that’s becoming increasingly likely as more and more people work from home during and after the pandemic.
- Denial-of-Service Attacks: These assaults overload systems, servers or networks with traffic to exhaust resources or bandwidth, leading to a fulfillment disruption of legitimate requests. These sorts of attacks were used to great effect by Anonymous earlier this year to take down the Minneapolis Police Department site.
- Structured Query Language (SQL) Injection: A less common form of attack which occurs when an attacker inserts malicious code into a server that uses SQL and forces it to reveal proprietary information.
- Zero-Day Exploit: Hits after a network vulnerability is announced but before a solution is implemented. These types of vulnerabilities are the least excusable on behalf of a data centre security team.
The need for physical and digital convergence
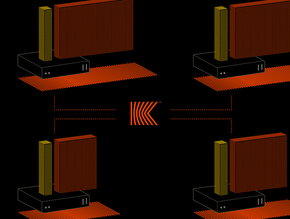
According to Scott Borg, Director of the U.S. Cyber Consequences Unit, “As long as organisations treat their physical and cyber domains as separate, there is little hope of securing either one. The convergence of cyber and physical security has already occurred at the technical level. It is long overdue at the organisational level.”
The separation between the cameras, motion sensors, locks and other physical elements of a data centre’s security architecture, and its firewall, encryption protocols and other digital defences creates a glaring vulnerability in a disturbing proportion of networks. “Right now, most US companies rely on patchwork systems, even to handle their most sensitive data and functions,” said Brivo CEO Steve Van Till in an interview back in April. “Now that we are experiencing the formerly unthinkable, security threats, both cyber and physical, have been illuminated or exacerbated and the importance of efficient, integrated, and secure systems has been highlighted.”
As with data centre power systems, the meeting point between the physical world and the digital one that is creating these vulnerabilities stems largely from the IoT. The number of new IoT devices grew by 7bn between 2018 and 2019, and that trend is only expected to accelerate. Many third party IoT sensors and systems operate without adequate cybersecurity built in. Finding ways to protect and isolate these devices from the core network is becoming an increasingly high priority for data centre operators, particularly as more and more IT activity is moved closer to the edges of networks.
The global IoT explosion is predicted to accelerate data centre cyber security spending significantly. Back in 2019, internet performance company Dyn was the main target of an attack by the Mirai botnet, “which basically goes into folks' homes and takes over Internet of Things devices and literally turns them into attack vectors," said Kyle York, Chief Strategy Officer at Dyn, in a news report for NBC.
According to Grand View Research, with the increase in cyber attacks, the demand for the global data centre security market will grow — with annual spending rising as high as $15.5bn a year by 2024. In a post-pandemic world, data centre operators will need to elevate their efforts even further in order to deal with more distributed networks, more unsecured smart devices, and increasing waves of cyber crime (which has grown into an estimated $600bn industry worldwide); the once-impenetrable castle has become a sprawling metropolis, and that sort of landscape requires a very different approach.